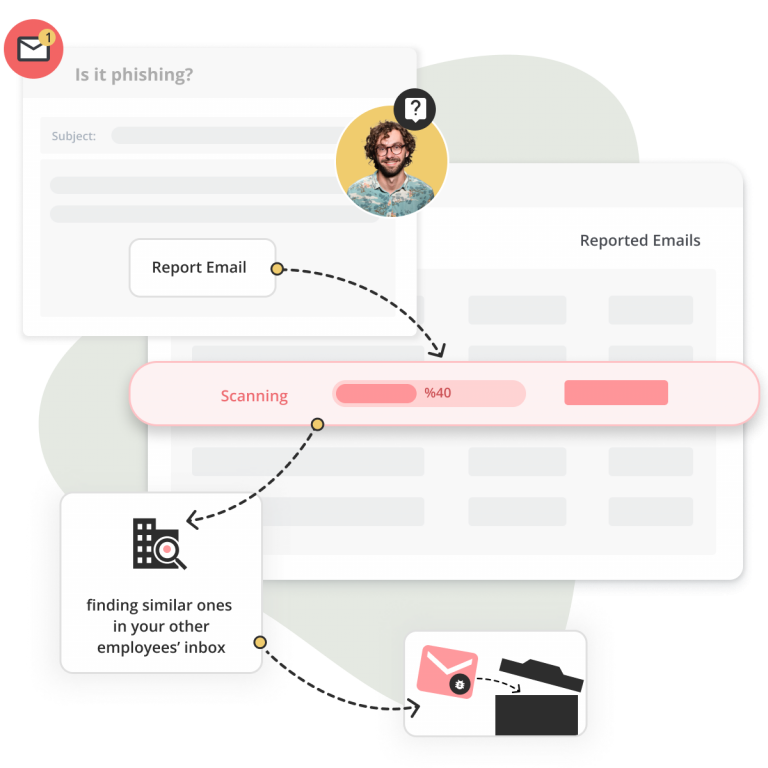
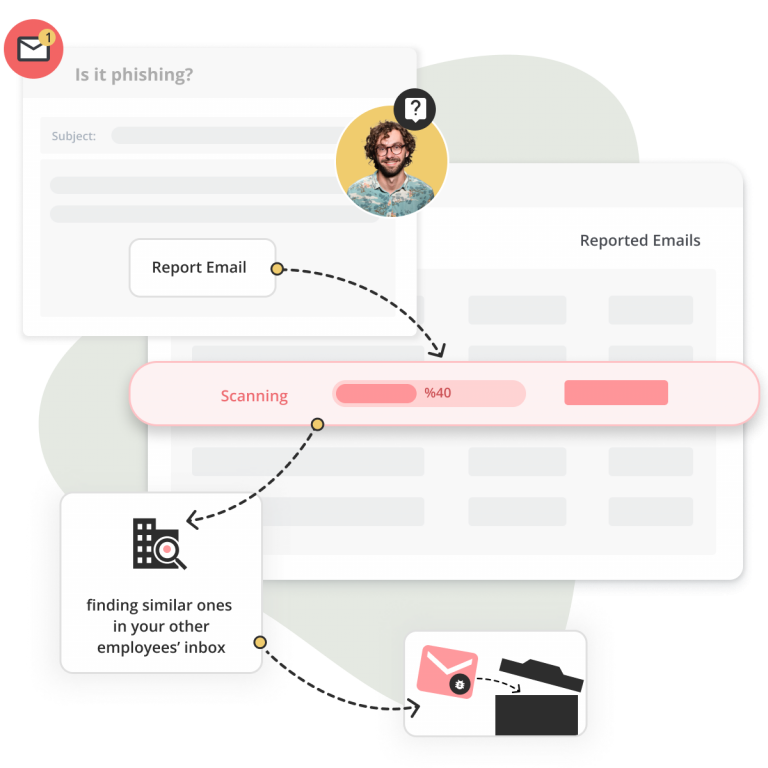
Automate your process
Customizable Playbook features enable you to create rules to classify reported email by header, body and attachment, allowing the system to easily analyze the technical criteria needed to identify malicious activity.
No expert skill set is needed to create rules to classify suspicious email and automate the appropriate response.